Ricoh introduces RansomCare
March 25, 2021
 Ricoh USA, Inc. announced RansomCare, its new Ransomware Containment Solution, technology that helps to stop ransomware attacks, which is one of the top security threats to businesses in the U.S. and around the world.
Ricoh USA, Inc. announced RansomCare, its new Ransomware Containment Solution, technology that helps to stop ransomware attacks, which is one of the top security threats to businesses in the U.S. and around the world.
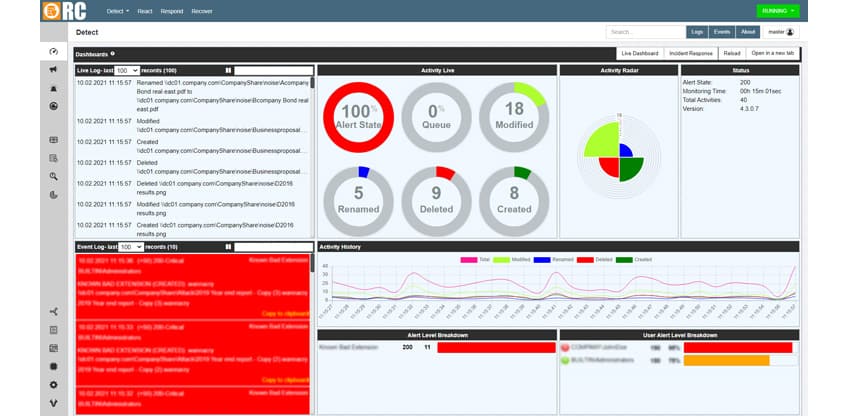
As a final line of defence, RansomCare’s multi-layered security detects, identifies, contains and isolates ransomware outbreaks at the source, limiting their significant impact on data integrity, system downtime, company-wide productivity and overall operations.
“With ransomware attacks continuing to deliver devastating impacts to companies, it’s not enough to have traditional protection practices as your sole line of defense,” said John A. Stewart, Vice President, IT Sales and Strategy, Ricoh USA, Inc. “Ricoh’s RansomCare is a vital element to an overall in-depth defence security strategy and acts as a last line of defence to stop an attack in near real-time, thus mitigating the impact and cost of a full attack for what is a fraction of what a ransom and/or downtime could cost.”
Capable of infecting up to 10,000 files per minute per infected device, ransomware is a form of malicious software, or malware, that encrypts files and documents, and holds computers and data files hostage, drastically impacting downtime, contributing to data loss, locking down entire networks and bringing business to a halt.
RansomCare provides peace of mind that business data is protected from cyberattack with advanced, integrated tools for comprehensive data protection, including:
- Active file monitoring to detect known and unknown ransomware variants and immediately alert security administrators of threats;
- Quick response to infected devices to halt illegitimate encryption, preventing mass spreading to files and reducing risk of expensive recovery efforts;
- Informed recovery of impacted files, simplifying backup restoration and logging attack details for additional insight;
- Detailed reporting, including exact time of attack, compromised users and devices, affected files and owners, and easily exported incident reporting for key stakeholders and data authorities.
Ricoh’s RansomCare, powered by Bullwall, monitors networks in near real time using multiple detection tactics to instantly detect the tell-tale signs that ransomware is at work. RansomCare responds by isolating and quarantining the compromised user and quickly identifying encrypted files to restore them from backup while automating any necessary incident reporting.
RansomCare complements existing endpoint protection platforms, and endpoint detection and response tools. RansomCare is easy to implement, with no discernible impact on network performance, requires no local agents or server applications, integrates seamlessly into existing security applications, offers built-in multi-alerting services to keep users apprised of risks and details exact files that require attention or restoration for security system administrators.
Categories : Products and Technology
Tags : Cybersecurity RansomCare Ransomware Ricoh